Firewalls and Intrusion Detection Systems: The Backbone of Modern Network Security
The modern digital world runs on interconnected systems, cloud platforms, online services, and global networks. Businesses, government agencies, and individuals depend heavily on internet-based technologies to store information, communicate, and operate essential services. However, this growing digital connectivity has also created new opportunities for cybercriminals to exploit vulnerabilities in computer networks. Data breaches, ransomware attacks, and unauthorized system access have become increasingly common across industries. Because of this, organizations must implement strong Network Firewall Intrusion Detection to defend their networks and protect sensitive data.
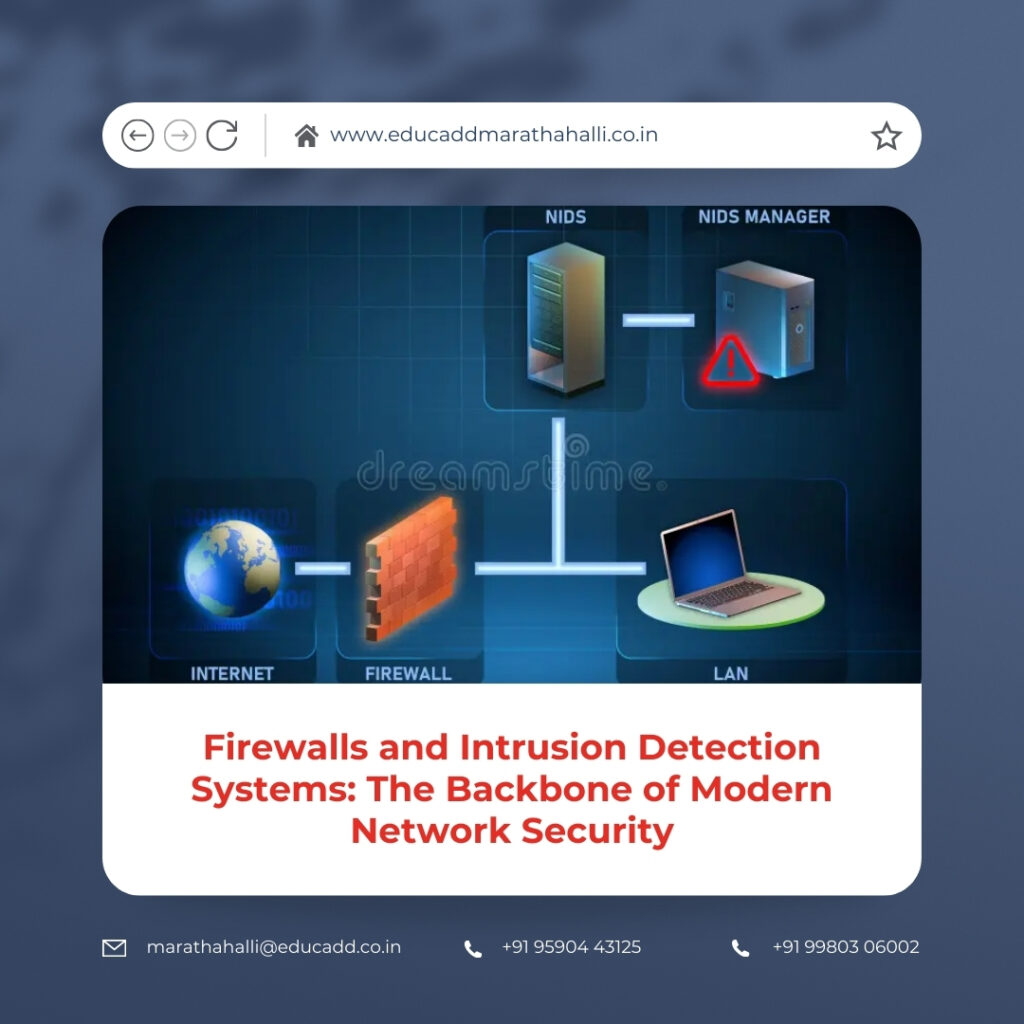
Two of the most important technologies used in network security are firewalls and intrusion detection systems. These tools form the foundation of many cybersecurity strategies by helping organizations monitor, filter, and analyze network traffic. A firewall acts as a protective gateway that controls what data enters or leaves a network. At the same time, an intrusion detection system constantly examines network activity to identify unusual or potentially harmful behavior. When these technologies work together, they create a powerful defensive structure that reduces the risk of cyberattacks.
Network Firewall Intrusion Detection
Understanding how firewalls and intrusion detection systems operate is essential for IT professionals, cybersecurity analysts, and organizations seeking to build secure networks. These technologies not only help prevent unauthorized access but also provide valuable insights into network behavior and potential threats. By implementing them effectively, businesses can safeguard their digital infrastructure and maintain trust with customers and partners.
The Rising Need for Strong Cybersecurity Measures
As digital transformation accelerates across industries, organizations increasingly rely on networked systems to perform daily operations. Online banking, e-commerce platforms, healthcare databases, and cloud services all require secure network environments to function safely. Unfortunately, the same networks that enable convenience and efficiency also present opportunities for cybercriminals.
Cyber threats have evolved significantly over the past decade. Attackers now use sophisticated techniques to bypass traditional security measures and gain access to valuable information. These threats include malware infections, phishing attacks, data breaches, and advanced persistent threats. Even a small security weakness can allow attackers to infiltrate a network and compromise critical systems.
The consequences of such attacks can be severe. Businesses may face financial losses, regulatory penalties, operational disruptions, and damage to their reputation. Therefore, organizations must prioritize network protection and adopt multiple layers of defense. Firewalls and intrusion detection systems play a vital role in this defensive approach by monitoring network traffic and identifying suspicious activities before they escalate into serious security incidents.
What Is a Firewall and Why It Matters
A Network Firewall Intrusion Detection is a security device or software application that monitors and regulates network traffic based on predetermined security rules. It acts as a boundary between a trusted internal network and untrusted external networks, such as the internet. By controlling which data packets can enter or leave the network, a firewall helps prevent unauthorized access to internal systems.
When data travels across a network, it moves in small units known as packets. Each packet contains information about its origin, destination, and type of communication. A firewall examines these packets and compares them with established security policies. If the packet meets the required conditions, the firewall allows it to pass through. If it violates the rules, the firewall blocks it.
Firewalls play a crucial role in maintaining network security because they create a controlled gateway between internal resources and external environments. Without a firewall, networks would remain exposed to countless threats originating from the internet. By filtering traffic and enforcing strict policies, firewalls significantly reduce the risk of unauthorized access and malicious activity.
Different Categories of Firewalls in Network Protection
Several types of firewalls exist, and each one offers unique capabilities for managing network security. Organizations often choose the type of firewall that best suits their infrastructure and security requirements.
Packet-filtering firewalls represent one of the earliest firewall technologies. These firewalls analyze packets based on attributes such as source address, destination address, port number, and communication protocol. Although this method provides basic protection, it may not detect complex threats.
Stateful inspection firewalls offer a more advanced approach by monitoring active network connections. Instead of evaluating each packet independently, these firewalls track the state of communication sessions. This allows them to determine whether packets belong to legitimate connections or suspicious activities.
Proxy firewalls operate differently by acting as intermediaries between internal users and external servers. When users request data from external websites, the proxy firewall processes the request on their behalf. This method hides internal network information and adds an extra layer of protection.
Next-generation firewalls combine traditional firewall functions with advanced security capabilities such as deep packet inspection, application awareness, and intrusion prevention. These modern systems provide comprehensive protection against complex cyber threats.
How Firewalls Defend Network Environments
Firewalls protect network environments by enforcing strict access control mechanisms. These mechanisms define what type of traffic is permitted and what should be blocked. By controlling communication pathways, firewalls prevent unauthorized users from accessing sensitive resources.
For example, organizations often restrict certain network ports that attackers commonly exploit. By blocking unnecessary ports, the firewall reduces potential entry points for malicious actors. Firewalls can also limit access to specific IP addresses or geographic regions, depending on the organization’s security requirements.
Another key feature of firewalls involves traffic logging and monitoring. Every connection attempt is recorded, allowing administrators to analyze patterns and identify suspicious behavior. These logs provide valuable insights into attempted attacks and potential vulnerabilities within the network.
Through continuous monitoring and rule enforcement, firewalls act as a strong barrier against many forms of cyber threats.
Understanding Intrusion Detection Systems
While Network Firewall Intrusion Detection focus on controlling traffic flow, intrusion detection systems concentrate on identifying malicious activities within a network. An intrusion detection system continuously monitors network traffic, system events, and user behavior to detect potential security violations.
These systems analyze large volumes of data to identify patterns associated with cyberattacks. When suspicious activity is detected, the intrusion detection system generates alerts that notify security teams about the possible threat.
Intrusion detection systems are particularly valuable because some attacks manage to bypass traditional security barriers. Even if malicious traffic enters the network, the intrusion detection system can still recognize abnormal behavior and alert administrators.
By providing real-time insights into network activity, intrusion detection systems help organizations respond quickly to potential security incidents and reduce the impact of cyberattacks.
Types of Intrusion Detection Systems
Intrusion detection systems can be categorized based on how and where they monitor network activity. The two most common types are network-based intrusion detection systems and host-based intrusion detection systems.
Network-based intrusion detection systems monitor traffic flowing across network segments. They analyze packets traveling through switches and routers to detect suspicious patterns. Because they observe network-wide activity, these systems provide a broad view of potential threats.
Host-based intrusion detection systems operate directly on individual computers or servers. These systems monitor operating system logs, application activity, and file integrity to identify unauthorized changes. They provide detailed visibility into the behavior of specific devices.
Another classification method focuses on detection techniques. Signature-based systems compare network activity against a database of known attack signatures. Anomaly-based systems identify unusual behavior that deviates from established patterns.
Each method contributes to a more comprehensive approach to threat detection.
How Intrusion Detection Systems Detect Cyber Threats
Intrusion detection systems rely on several analytical methods to recognize malicious activity. One common method involves signature-based detection. This technique compares network events against a database of previously identified attack patterns. When a match occurs, the system generates an alert.
Another method involves anomaly detection. In this approach, the system learns normal network behavior over time and establishes a baseline. Any activity that deviates significantly from this baseline may indicate a potential attack.
For instance, if a user account suddenly attempts to access hundreds of files within seconds, the intrusion detection system may identify this behavior as suspicious. Security teams can then investigate the event and determine whether it represents a genuine threat.
By combining multiple detection techniques, intrusion detection systems improve the accuracy of threat identification and reduce the chances of undetected attacks.
Key Differences Between Firewalls and Intrusion Detection Systems
Although both technologies contribute to network security, firewalls and intrusion detection systems perform distinct roles. Firewalls primarily control access by filtering traffic based on predefined rules. Their goal is to prevent unauthorized connections from entering the network.
Intrusion detection systems, however, focus on analyzing activities that occur within the network. Instead of blocking traffic directly, they detect suspicious behavior and notify administrators.
Another difference lies in how these technologies operate within network architecture. Firewalls are typically positioned at network gateways, where internal networks connect to external environments. Intrusion detection systems may operate at multiple points within the network to observe both external and internal traffic.
Together, these technologies create a layered security strategy that enhances overall protection.
Combining Firewalls and Intrusion Detection Systems for Stronger Security
Organizations achieve stronger network protection when they integrate firewalls and intrusion detection systems into a unified security framework. Each technology addresses different aspects of cybersecurity, and their combined use creates multiple layers of defense.
For example, a Network Firewall Intrusion Detection may block unauthorized traffic attempting to enter the network. However, if an attacker manages to bypass this barrier, the intrusion detection system can still detect abnormal behavior within the network.
Some modern security solutions allow these technologies to work together automatically. When the intrusion detection system detects suspicious activity, it can instruct the firewall to block the attacker’s IP address. This coordinated response improves the speed and effectiveness of threat mitigation.
Through this integration, organizations can identify and stop cyber threats more efficiently.
Advantages of Deploying Firewalls and Intrusion Detection Systems
The implementation of firewalls and intrusion detection systems offers numerous advantages for organizations seeking to protect their digital assets. One major benefit involves enhanced visibility into network activity. Administrators gain detailed insights into traffic patterns, user behavior, and system interactions.
Another advantage is improved threat prevention. Firewalls block many malicious connections before they reach internal systems, while intrusion detection systems identify suspicious activities that may indicate ongoing attacks.
These technologies also support regulatory compliance. Many industries require organizations to implement security controls that protect sensitive information such as financial data or personal records.
Additionally, strong network security helps maintain business continuity. By detecting and preventing attacks early, organizations reduce downtime and avoid costly disruptions.
Challenges Associated with Network Security Monitoring
Despite their benefits, firewalls and intrusion detection systems require careful management. Improper configuration can reduce their effectiveness or disrupt legitimate network activities.
One challenge involves false positives. Intrusion detection systems may sometimes interpret normal network behavior as suspicious activity. When too many alerts occur, security teams may struggle to identify genuine threats.
Another challenge involves maintaining updated security rules and signatures. Cyber threats evolve constantly, and security tools must receive regular updates to remain effective.
Large organizations may also face complexity when managing multiple security devices across distributed networks and cloud environments. Coordinating policies and monitoring alerts across these systems requires skilled cybersecurity professionals.
Addressing these challenges is essential for maintaining a reliable security infrastructure.
Best Practices for Implementing Network Security Systems
Organizations should follow several best practices to ensure the effective deployment of firewalls and intrusion detection systems. The first step involves developing a clear network security policy that defines access permissions and security rules.
Administrators should regularly review firewall configurations to ensure they align with current security requirements. Removing unnecessary open ports and restricting access to critical systems can significantly reduce attack risks.
Continuous monitoring also plays an important role. Security teams should review alerts, analyze traffic logs, and investigate unusual activities promptly.
Routine software updates and threat intelligence integration are equally important. By keeping detection databases up to date, organizations ensure that their systems can recognize newly discovered attack patterns.
Finally, regular security audits and penetration testing help identify vulnerabilities and strengthen overall defenses.
The Future of Network Security Technologies
The cybersecurity landscape continues to evolve as new technologies emerge and cyber threats grow more sophisticated. Artificial intelligence and machine learning are increasingly being integrated into security systems to enhance threat detection capabilities.
These technologies allow intrusion detection systems to analyze vast amounts of data and recognize subtle patterns associated with cyberattacks. Automated responses can also reduce reaction time during security incidents.
Cloud computing and remote work environments are also shaping modern network security strategies. Many organizations now deploy cloud-based firewalls and detection systems to protect distributed networks and remote users.
As digital infrastructures expand, advanced security solutions will play an even more critical role in safeguarding networks against evolving cyber threats.
Conclusion
Network Firewall Intrusion Detection systems form the foundation of modern network security strategies. Firewalls serve as protective gateways that regulate network traffic and prevent unauthorized access to internal systems. Intrusion detection systems complement this protection by monitoring network activity and identifying suspicious behavior that may indicate cyberattacks.
Together, these technologies create a multi-layered defense that helps organizations detect, prevent, and respond to security threats effectively. By implementing firewalls and intrusion detection systems as part of a comprehensive cybersecurity strategy, businesses can protect sensitive information, maintain operational stability, and strengthen trust with customers and partners.
As cyber threats continue to evolve, organizations must remain proactive in strengthening their security infrastructure. Continuous monitoring, regular updates, and the adoption of advanced security technologies will ensure that networks remain protected in an increasingly connected digital world.
